New Federal Cybersecurity Regulations: Q3 2026 Impact on 1.5 Million US Businesses

Anúncios
Breaking news has sent ripples through the business community: new Federal Cybersecurity Regulations are on the horizon, poised to significantly impact an estimated 1.5 million US businesses by Q3 2026. This isn’t just another compliance update; it’s a fundamental shift in how organizations are expected to protect their digital assets and sensitive data. For many businesses, particularly small and medium-sized enterprises (SMEs), these impending regulations represent both a formidable challenge and a critical opportunity to bolster their cybersecurity posture. The clock is ticking, and understanding the scope, implications, and necessary steps for compliance is paramount.
The digital landscape is constantly evolving, with cyber threats growing in sophistication and frequency. In response, federal agencies are tightening the reins, recognizing that a fragmented approach to cybersecurity leaves too many vulnerabilities. The new Federal Cybersecurity Regulations aim to create a more unified, resilient, and secure digital environment across various sectors. While specific details are still being finalized, the overarching goal is clear: to establish a baseline of robust cybersecurity practices that all affected businesses must adhere to. This means a proactive approach, rather than a reactive one, will be essential for survival and success in the modern economy.
Anúncios
For 1.5 million US businesses, the period leading up to Q3 2026 will be a race against time. Companies will need to assess their current cybersecurity frameworks, identify gaps, implement new technologies, and educate their workforce. Failure to comply could result in substantial penalties, reputational damage, and a loss of trust from customers and partners. This article delves deep into these upcoming regulations, providing an essential guide for businesses to navigate this complex terrain and emerge stronger and more secure.
Anúncios
The Impetus Behind New Federal Cybersecurity Regulations
Why now? The surge in cyberattacks, coupled with the increasing interconnectedness of global supply chains and critical infrastructure, has created an urgent need for more stringent cybersecurity measures. High-profile data breaches, ransomware attacks, and nation-state sponsored cyber espionage have highlighted the vulnerabilities inherent in existing systems. The economic and national security implications of these incidents are immense, prompting federal lawmakers and agencies to act decisively. The new Federal Cybersecurity Regulations are a direct response to these escalating threats, aiming to fortify the nation’s digital defenses from the ground up.
Escalating Cyber Threats and Economic Impact
Recent years have seen an unprecedented rise in cybercrime. Ransomware attacks, in particular, have crippled businesses, healthcare systems, and government agencies, often demanding exorbitant sums for data recovery. Phishing schemes, supply chain attacks, and zero-day exploits continue to evolve, making it increasingly difficult for organizations to stay ahead of malicious actors. The financial toll of these attacks is staggering, running into billions of dollars annually, not to mention the irreparable damage to reputation and customer trust. These staggering costs and widespread disruptions have underscored the need for a standardized, enforceable set of cybersecurity guidelines.
Protecting Critical Infrastructure and Supply Chains
Beyond individual businesses, the new regulations also seek to protect critical infrastructure sectors (energy, water, transportation, healthcare) and their intricate supply chains. A breach in one part of the system can have cascading effects, potentially jeopardizing national security and public safety. By mandating stronger cybersecurity practices across a broad spectrum of businesses, the federal government aims to build a more resilient ecosystem that can withstand sophisticated attacks. This holistic approach recognizes that the weakest link in a supply chain can expose the entire network to risk.
Harmonizing and Standardizing Cybersecurity Practices
Currently, the US cybersecurity landscape is characterized by a patchwork of state-specific laws, industry-specific regulations (like HIPAA for healthcare or PCI DSS for payment card data), and voluntary frameworks. While these have served their purpose, they often lead to confusion, duplication of effort, and inconsistent levels of protection. The new Federal Cybersecurity Regulations aim to harmonize and standardize these practices, providing a clearer, more consistent framework for compliance. This standardization is expected to simplify compliance for businesses operating across multiple jurisdictions and sectors, ultimately raising the baseline security posture for all.
Who Will Be Affected? The 1.5 Million US Businesses
The broad scope of these regulations is perhaps their most defining characteristic. While the exact criteria for inclusion are still being refined, initial estimates suggest that approximately 1.5 million US businesses will fall under their purview. This includes a significant number of small and medium-sized enterprises (SMEs) that may not have dedicated cybersecurity teams or extensive resources. Understanding whether your business will be affected is the first critical step toward compliance.
Defining the Scope: Beyond Large Enterprises
Historically, federal cybersecurity regulations have often focused on large corporations, government contractors, and highly regulated industries. However, the new framework is expected to cast a wider net. It’s anticipated to encompass businesses that handle sensitive customer data, operate critical infrastructure components, or are part of essential supply chains, regardless of their size. This shift acknowledges that even small businesses can be attractive targets for cybercriminals and serve as gateways into larger networks.
Key Indicators for Impacted Businesses
- Data Handled: Businesses processing or storing personally identifiable information (PII), protected health information (PHI), financial data, or other sensitive customer/employee data.
- Industry Sector: Companies operating in critical infrastructure sectors (e.g., manufacturing, energy, finance, healthcare, IT, communications, transportation, water).
- Government Contracts: Businesses that contract with federal agencies, even as subcontractors.
- Supply Chain Role: Organizations that are integral to the supply chains of larger, regulated entities.
- Revenue/Employee Thresholds: While not the sole determinant, some regulations may include thresholds based on annual revenue or number of employees, though these are likely to be set to include many SMEs.
Businesses should proactively assess their operations against these indicators. If there’s any doubt, consulting with legal and cybersecurity experts will be crucial to determine the applicability of the new Federal Cybersecurity Regulations to their specific context.

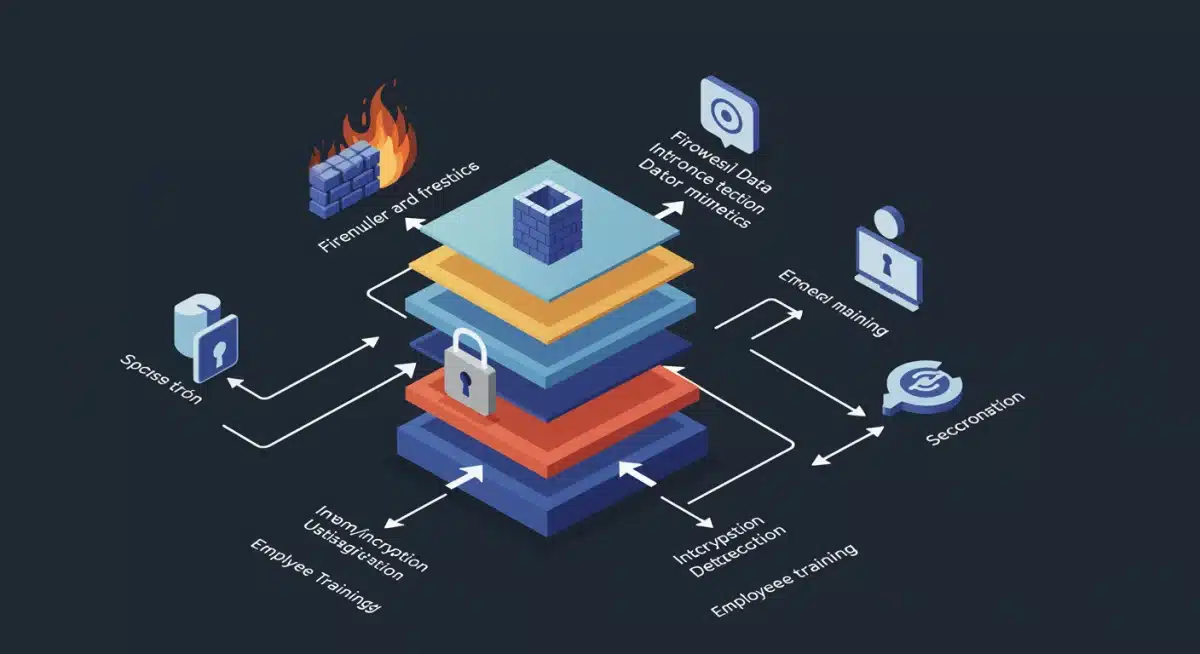
Key Pillars of the New Federal Cybersecurity Regulations
While the final text of the regulations is still pending, industry experts and leaked drafts suggest several core pillars that will form the foundation of these new requirements. These pillars are designed to create a comprehensive and robust cybersecurity program within affected organizations.
1. Robust Risk Management Frameworks
A cornerstone of the new regulations will undoubtedly be the requirement for businesses to implement and maintain a comprehensive risk management framework. This isn’t just about identifying risks; it’s about systematically assessing, prioritizing, and mitigating them. This typically involves:
- Regular Risk Assessments: Conducting periodic evaluations to identify potential cyber threats and vulnerabilities.
- Asset Identification: Cataloging all critical IT assets, data, and systems.
- Risk Treatment Plans: Developing strategies to address identified risks, whether through acceptance, avoidance, transfer (e.g., cyber insurance), or mitigation.
- Continuous Monitoring: Implementing systems to continuously monitor for new threats and vulnerabilities.
2. Mandatory Incident Reporting and Response
Timely and accurate incident reporting will be a critical component. Businesses will likely be required to report significant cyber incidents to appropriate federal agencies within a specified timeframe. This allows for better threat intelligence sharing and coordinated responses. Beyond reporting, organizations will need:
- Incident Response Plans: Documented procedures for detecting, analyzing, containing, eradicating, recovering from, and post-incident review of cyber incidents.
- Designated Response Teams: Clearly defined roles and responsibilities for incident response.
- Communication Protocols: Plans for communicating with stakeholders, including customers, regulators, and law enforcement, during and after a breach.
3. Data Protection and Encryption Standards
Protecting sensitive data will be front and center. The regulations are expected to mandate specific data protection measures, including:
- Encryption: Requirements for encrypting sensitive data both in transit and at rest.
- Access Controls: Implementing robust access controls (e.g., multi-factor authentication, least privilege access) to prevent unauthorized data access.
- Data Minimization: Encouraging practices to collect and retain only necessary data.
- Data Lifecycle Management: Securely managing data from creation to destruction.
4. Supply Chain Security
Recognizing that many cyberattacks originate through third-party vendors, the new regulations will likely place significant emphasis on supply chain security. Businesses will be responsible for ensuring that their vendors and partners also adhere to appropriate cybersecurity standards. This could involve:
- Vendor Risk Assessments: Vetting third-party vendors for their cybersecurity posture.
- Contractual Requirements: Including specific cybersecurity clauses in vendor contracts.
- Monitoring Third-Party Access: Overseeing and restricting vendor access to internal systems and data.
5. Employee Training and Awareness
Human error remains a leading cause of data breaches. Consequently, the regulations will likely require regular and comprehensive cybersecurity training for all employees. This includes:
- Phishing Awareness: Training employees to recognize and report phishing attempts.
- Password Hygiene: Educating on best practices for strong passwords and multi-factor authentication.
- Data Handling Policies: Ensuring employees understand proper procedures for handling sensitive information.
- Regular Refresher Courses: Conducting ongoing training to keep employees informed about new threats and policies.
6. Regular Audits and Assessments
To ensure ongoing compliance, businesses will likely be required to undergo regular cybersecurity audits and assessments, either internally or by third-party experts. These audits will verify the effectiveness of implemented controls and identify areas for improvement. This could include vulnerability scanning, penetration testing, and compliance audits against the new regulatory framework.
Challenges and Opportunities for Businesses
The introduction of these new Federal Cybersecurity Regulations will undoubtedly present both significant challenges and unique opportunities for the 1.5 million affected businesses.
Navigating the Compliance Maze: Key Challenges
- Resource Allocation: Many SMEs lack the financial resources and in-house expertise to implement complex cybersecurity measures. Hiring skilled cybersecurity professionals or engaging external consultants can be costly.
- Complexity of Requirements: The technical nature of some regulations may be overwhelming for businesses without a strong IT background. Understanding and interpreting the requirements will be a hurdle.
- Legacy Systems: Older IT infrastructure may not be compatible with modern security controls, requiring expensive upgrades or replacements.
- Data Volume and Diversity: Businesses handling vast amounts of diverse data will face immense challenges in categorizing, protecting, and monitoring it all effectively.
- Continuous Evolution of Threats: Cybersecurity is not a static field. Businesses will need to continuously adapt their defenses to counter evolving threats, which requires ongoing investment and vigilance.
Unlocking New Opportunities: The Upside of Compliance
- Enhanced Trust and Reputation: Demonstrating strong cybersecurity compliance can significantly boost customer trust and enhance a business’s reputation in the marketplace. This can be a key differentiator.
- Competitive Advantage: Businesses that proactively embrace the new regulations can gain a competitive edge, especially when partnering with larger organizations that prioritize secure supply chains.
- Reduced Risk of Breaches and Fines: Investing in compliance now can prevent costly data breaches, legal fees, regulatory fines, and business disruptions in the future.
- Improved Operational Efficiency: A well-structured cybersecurity program often leads to better IT governance, streamlined processes, and a clearer understanding of an organization’s digital assets.
- Innovation and Growth: By fostering a secure environment, businesses can confidently explore new digital initiatives, cloud adoptions, and market expansions without undue fear of cyber threats.
Proactive Steps for Businesses to Take Now
With Q3 2026 rapidly approaching, businesses cannot afford to wait for the final regulations to be published before taking action. Proactive preparation is key to ensuring a smooth transition and minimizing the impact of these new Federal Cybersecurity Regulations. Here are essential steps:
1. Conduct a Comprehensive Cybersecurity Audit
The first step is to understand your current cybersecurity posture. Engage a qualified third party or leverage internal expertise to conduct a thorough audit of your existing systems, policies, and procedures. Identify vulnerabilities, assess current controls, and pinpoint areas that will require significant improvement to meet anticipated federal standards.
2. Develop an Internal Task Force or Appoint a CISO
Designate a specific individual or team to lead your organization’s compliance efforts. For larger businesses, this might mean appointing a Chief Information Security Officer (CISO). For smaller businesses, it could be an IT manager or a dedicated consultant. This task force should be responsible for monitoring regulatory updates, developing compliance strategies, and overseeing implementation.
3. Invest in Employee Training and Awareness Programs
As mentioned, human error is a major vulnerability. Implement ongoing cybersecurity awareness training for all employees, from the executive suite to entry-level staff. Focus on recognizing phishing attempts, strong password practices, secure data handling, and reporting suspicious activities. Regular refreshers are crucial.
4. Review and Update Data Management Policies
Understand what sensitive data your business collects, where it’s stored, how it’s processed, and who has access to it. Implement data minimization principles, encrypt sensitive data, and establish clear data retention and destruction policies. Ensure robust access controls are in place, including multi-factor authentication (MFA) wherever possible.
5. Evaluate and Secure Your Supply Chain
Your cybersecurity is only as strong as your weakest link. Review your contracts and relationships with third-party vendors, suppliers, and service providers. Assess their cybersecurity practices, request proof of compliance with relevant standards, and consider adding cybersecurity clauses to all new and existing vendor agreements. Implement strict access controls for any third parties accessing your systems.
6. Modernize Infrastructure and Implement Security Technologies
Invest in up-to-date security technologies. This includes firewalls, intrusion detection/prevention systems (IDS/IPS), endpoint detection and response (EDR) solutions, security information and event management (SIEM) systems, and robust backup and disaster recovery solutions. Ensure your software and hardware are regularly updated and patched.
7. Develop and Test an Incident Response Plan
Don’t wait for a breach to discover you don’t have a plan. Develop a detailed incident response plan that outlines steps for detection, containment, eradication, recovery, and post-incident analysis. Crucially, regularly test this plan through tabletop exercises and simulations to identify weaknesses and ensure your team is prepared for a real-world cyberattack.
8. Engage Legal and Cybersecurity Experts
Given the complexity of these regulations, engaging with legal counsel specializing in cybersecurity law and experienced cybersecurity consultants is highly advisable. They can help interpret the requirements, assess your compliance posture, and guide you through the implementation process.
The Road Ahead: Q3 2026 and Beyond
The journey to full compliance with the new Federal Cybersecurity Regulations will be a continuous process, not a one-time event. As cyber threats evolve, so too will the regulatory landscape. Businesses must cultivate a culture of cybersecurity, embedding best practices into their daily operations and strategic planning. The deadline of Q3 2026 serves as a critical milestone, but the commitment to cybersecurity must extend far beyond it.
The federal government’s move to impose these comprehensive regulations underscores a crucial reality: cybersecurity is no longer an optional add-on but a fundamental requirement for doing business in the digital age. For the 1.5 million US businesses affected, embracing these changes proactively will not only ensure compliance but also build resilience, protect valuable assets, and foster greater trust with customers and partners. The investment made today in cybersecurity will pay dividends in the form of enhanced security, reduced risk, and sustained growth in an increasingly interconnected and threat-filled world.
Stay informed, stay prepared, and prioritize your digital defenses. The future of your business may depend on it.